Modeled through Signal Detection Theory + Threshold Model of Collective Behavior, within a Complex Adaptive System
How many cyber incidents does it take for an organization to believe it’s under attack? This post explores that psychological and systemic tipping point—bridging perception, decision science, and complex adaptive security behavior.

Who This Is For
- CISOs and security strategists
- Cyber resilience and risk management teams
- Researchers studying human factors in cybersecurity
Why It Matters (2025+)
Organizations today operate in information-dense threat landscapes—daily pings, false positives, and isolated attacks blur the line between noise and signal. Yet, a few strategically timed incidents can trigger an overreaction: “We’re being targeted.”
Understanding when perception crosses into collective belief is key to designing resilient incident response, avoiding panic, and maintaining operational continuity.
What You’ll Learn
- ✅ How Signal Detection Theory (SDT) models organizational sensitivity to threat cues
- ✅ How the Threshold Model of Collective Behavior explains “we’re under attack” moments
- ✅ How Complex Adaptive Systems (CAS) reveal emergent behaviors after perceived targeting
What Is the “Tipping Point of Perceived Targeting”?
It’s the psychological and systemic moment when an organization collectively believes it’s being singled out—regardless of objective evidence.
Like the “9/11 effect” in aviation or cascading panic in markets, perception becomes reality, driving policy shifts, communication freezes, and sometimes self-inflicted outages.
Theoretical Framework
Signal Detection Theory (SDT)
SDT separates signal (true attack) from noise (false alarms) through two parameters:
- Sensitivity (d’) – how well the organization distinguishes attacks from random noise
- Decision Criterion (β) – the internal threshold to declare “we’re under attack”
When false positives increase (due to noisy detection systems or heightened fear), the criterion shifts—triggering more alerts and anxiety.
Threshold Model of Collective Behavior (Granovetter, 1978)
Each individual (analyst, manager, exec) has a threshold for belief:
- Some react after the first event.
- Others wait until 3–4 peers share the same concern.
- When enough thresholds are crossed, a cascade forms → organizational consensus of targeting.
Complex Adaptive System (CAS) View
An organization is not linear—it’s a web of adaptive agents.
Once the “targeted” belief spreads:
- Information flow centralizes (CISO war rooms, exec updates)
- Normal operations pause (patch freezes, audit surges)
- Feedback loops reinforce the narrative (“see, another alert!”)
This emergent behavior mimics phase transitions in physics—small inputs leading to abrupt systemic change.
Modeling the Tipping Point
Variables:
- x: number of detected anomalies (signals)
- p(x): probability they’re correlated (perceived pattern)
- T: threshold of collective concern (fraction of org believing it’s targeted)
When:
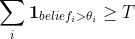
…the organization flips into “targeted” mode.
Simulating this in a CAS (e.g., using Python agent-based modeling) shows non-linear escalation—few incidents can shift the global state if network connectivity or trust is high.
Practical Implications
- Resilience Dashboards:
Visualize perceived threat density vs actual incident correlation.
Use anomaly dispersion metrics to prevent panic thresholds. - Decision Hygiene:
Train executives on SDT concepts—distinguish confidence from correlation.
Introduce “cognitive firewalls” to slow premature crisis declarations. - Collective Threshold Calibration:
Periodically recalibrate organizational belief thresholds based on recent event patterns, red-team drills, and communication lags.
Example Visualization (Concept)
Perceived Threat Intensity ─┐
│ ▄▄▆███
│ ▄██▀▀▀
│ ▄██▀
└──────────────→ Incident Count
↑ ↑
Normal Noise Tipping Point
Security Leadership Takeaways
- Model perception management as seriously as threat management.
- Use SDT metrics (d’, β) to tune detection systems and human escalation thresholds.
- Integrate behavioral science into cyber resilience strategy.
Resources & Links
- Granovetter, M. (1978). Threshold Models of Collective Behavior
- Wickens, C. D. (2002). Engineering Psychology & Human Performance
- Holland, J. H. (1992). Complex Adaptive Systems: A View from the Sciences
Final Thoughts
The tipping point of perceived targeting isn’t just about technology—it’s about cognition, communication, and collective thresholds.
Understanding these models can help CISOs prevent organizational overreactions and maintain resilience under uncertainty.
Stay ahead of the curve with secure AI and behavioral insights. For more deep-dives, visit SecureBytesBlog.com.
Subscribe to SecureBytesBlog for more thought leadership on security psychology and resilience modeling.
